
Entra ID Governance is here, another arrow in the quiver of the Microsoft Entra product family. This new solution is designed to help businesses better navigate the fine balance between productivity and security, all the while improving compliance with regulatory requirements. Matt Fernandes, Solutions Architect, explores what’s new, and how to leverage it.
Entra is now made up of several products. At its core is Entra ID (formally Azure Active Directory) and readers will be pleased to know that nothing has changed here except the name.
So what does Entra ID Governance bring to the table? Have a look at the pricing matrix here and you will see that it is a brand new SKU, however almost all of the features of the separate SKU are included in Entra ID P2, only the really juicy bits are missing.
- Machine learning assisted access certifications and reviews
- Entitlement management with Verified ID
- Lifecycle workflows
- The new Identity Governance Dashboard
Machine Learning Assistance
This has been around since the start of the year and gives the option to enable recommendations for decision makers during the review process. A nice easy one is the “No sign-in within 30 days”, mostly very helpful. The new “User-to-Group Affiliation” is where more of the magic happens.
The User-to-Group Affiliation recommendation compares users’ relative affiliation with other users in the group, based on the organisation’s reporting structure. Microsoft’s machine learning based scoring mechanism identifies the distance between the users in the tree to detect those users who are very distant from other users in the group. If the user has a “low affiliation” then the system recommends a ‘Deny’ result.
Entitlement management with Verified ID
When configuring access package policies, admins can specify who it’s for, users in the directory, connected organisations, or external users. Entitlement Management then determines if the person requesting the access package is within the scope of the policy.
In certain circumstances you might need users to present additional identity proofs during the request process such as a training certification or work authorisation.
Access package managers can require that requestors present a Verified ID containing those credentials from a trusted issuer. Approvers can then quickly view if a user’s verifiable credentials were validated at the time that the user presented their credentials and submitted the access package request.
Lifecycle workflows
Lifecycle workflows are a new identity governance feature that enables organisations to manage Azure Active Directory (Azure AD) users by automating these three basic lifecycle processes:
- Joiner: When an individual enters the scope of needing access.
- E.g. a new employee joining an organisation.
- Mover: When an individual moves between boundaries within an organisation.
- E.g. a user who was in marketing and is now a member of the sales organisation.
- Leaver: When an individual leaves the scope of needing access.
- E.g. an employee who’s retiring or an employee who’s terminated.
Traditionally services such as Sailpoint, Hitachi ID or Microsoft Identity Manager would be used to create complex and obscure rules written in C#, Python or other code language that requires skill and experience to build, troubleshoot, and maintain.
Entra ID Lifecycle Workflows are the cloud-based solution to this. Workflows consist of execution conditions (what needs to be in place for anything to happen) and tasks (the thing that actually gets done).
Here’s an example. Someone new is joining the business but they have a very long notice period. Their new manager is so busy that they forget all about their new starter. Fortunately, their IT Admins set up the joiner workflow below:
- Task
- Send Email
- Scope
- New Employees (based on the “employeeHireDate” attribute)
- Trigger
- Seven days before “employeeHireDate” attribute value
This email contains details about the new starter, information on obtaining the correct hardware for them and even a one-time password that the new employee can use to log straight into their new equipment dramatically reducing the onboarding time.
Lifecycle workflows will integrate with Logic Apps so can be extended into more complex scenarios in a lowcode / nocode format.
This is an exciting area for those looking for a cloud first identity approach, providing an opportunity to rely less on on-premises infrastructure and the “black box” that sits in the corner doing “something.”
Governance Dashboard
The aim of the new Microsoft Entra ID Governance dashboard is to pull information together that gives you an overview of your Identity Governance, act as a launch-pad for IGA features, and give quick access to compliance reports.
Implementing Identity Governance is a journey, naturally, everyone is at different stages of this journey and the ID Governance Dashboard provides different value for these nuances.
- Just getting started.
- The dashboard helps you assess the complexity of your identity landscape. Discover the number of users and guests in your tenant, as well as applications and privileged roles. Use this information combined with a review of other capabilities in Entra ID Governance to create an implementation plan that addresses your security and compliance requirements.
- Part way through your adventure.
- If you have already deployed one or more of the Entra ID Governance features, you can use the dashboard to understand the coverage of your governance automations. This information can help you to find and close gaps. For example, perhaps you have implemented birthright access using the entitlement management features but have not yet configured access reviews. The dashboard highlights this in an intuitive format and provides links to help you get started.
The dashboard experience is made up of the following main components:
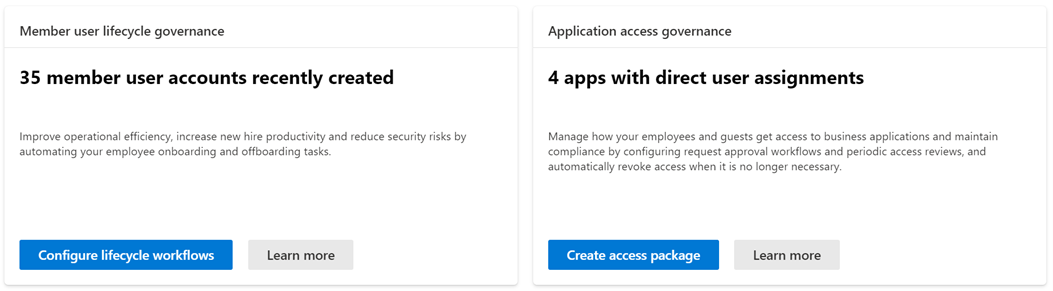
Glanceable cards: These cards provide high-level insights into what is happening in your tenant from the perspective of employee, guest, privileged identities, and application access governance. The cards also have links that point to quick start guides and tutorials.
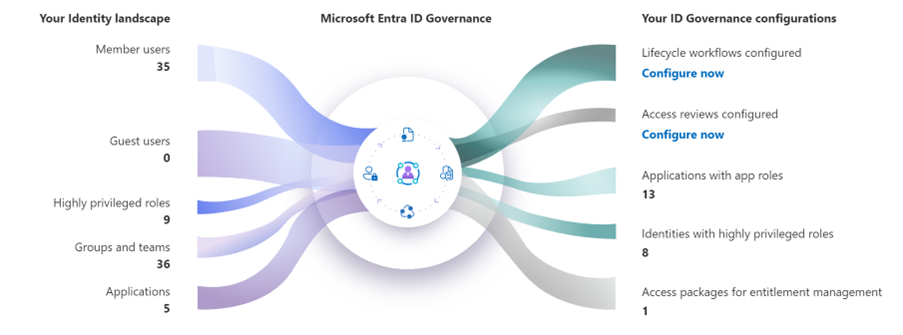
ID Governance status: This visual shows your identity landscape with quick glance metrics for number of employees, guests, business apps, groups, and privileged roles. It also highlights which Microsoft Entra ID Governance feature sets are still to be configured. If a feature is not configured, you can use the “Configure Now” option to get started.
Tutorials: This section contains tutorials of popular ID Governance use cases for quick access.
Highlights: Keep up to date with the latest ID Governance features and learn how others are using the tools to improve their security and compliance posture.
A whistle-stop tour I know, but one that I hope shows some of the exciting possibilities these new features will bring, especially when you look further ahead on the roadmap as Microsoft push for Cloud First source of authority and identity management. Lifecycle Workflows in particular interest me as it is real acknowledgement that low code / no code is being embraced by the identity security community and I am very much looking forward to the amazing solutions that the community create.
ID Governance extends the market-leading identity and access management platform in Azure Active Directory. It’s easy to deploy and includes capabilities for meeting compliance requirements with ML powered access review recommendations, a no-code/low-code approach for extensibility, workflows for automating identity lifecycle management tasks, and access provisioning for SaaS and on-premises applications, Microsoft
If you’d like to be updated about the Microsoft Entra product family and how Condatis is helping organisations evolve, sign up for our newsletter or speak to our team to discuss your business goals.
Get more content like this straight to your inbox!
Subscribe to stay up to date. You can unsubscribe at any time!